Real CoinDesk journalists don’t ask for money. Also, please be wary of links sent from people claiming to work for us.
Massive Solana Heist: CLINKSINK Drainer Campaigns Swipe Nearly $1M Worth Of SOL
In a recent report released by Mandiant, a threat intelligence and cybersecurity company, alarming details have emerged about the widespread exploitation of Solana users through a campaign known as CLINKSINK.
The report sheds light on the nature of these drainer campaigns, which have resulted in the loss of nearly $1 million worth of SOL tokens.
CLINKSINK Campaign Targets Solana Investors
According to the report, The CLINKSINK campaign, identified by Mandiant, involves malicious actors leveraging drainers – malicious scripts and smart contracts – to steal funds and digital assets, including non-fungible tokens (NFTs), from unsuspecting victims’ cryptocurrency wallets.
These campaigns have been active since December 2023 and have employed at least 35 affiliate IDs associated with a drainer-as-a-service (DaaS) utilizing CLINKSINK.
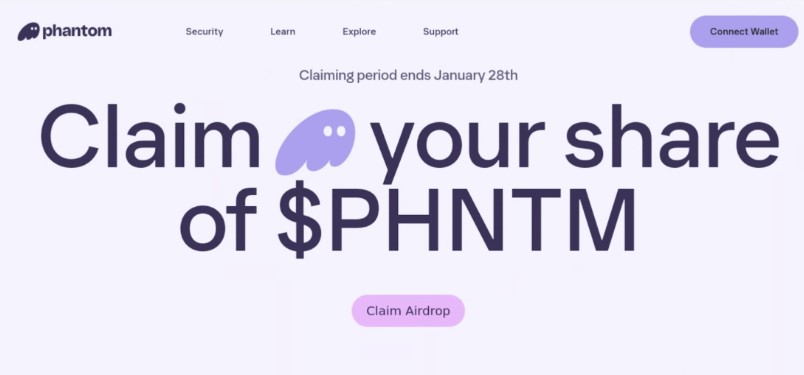
The modus operandi of the CLINKSINK campaign involves distributing cryptocurrency-themed phishing pages through social media platforms like X and chat applications like Discord.
These pages, masquerading as legitimate cryptocurrency resources like Phantom, DappRadar, and BONK, entice victims to interact with the CLINKSINK drainer. Once victims connect their wallets to claim an alleged token airdrop, they are prompted to sign a transaction that allows the drainer service to siphon funds from their wallets.
Mandiant’s investigation revealed that the stolen funds are divided between the affiliate and the service operator(s) based on a predetermined percentage.
The analysis indicates that, on average, 80% of the stolen funds go to the affiliate, while the remaining 20% go to the operator(s). However, the operator’s cut can vary between 5% and 25%, potentially influenced by factors such as partnerships or reduced fees for successful affiliates.
Since the end of December 2023, at least 1,491 SOL tokens and numerous underlying tokens, with a combined value of over $180,000, were traced to a specific Solana address associated with the DaaS operator.
Based on this data, Mandiant estimates that these recent campaigns have stolen at least $900,000 in digital assets. However, it is important to note that some of the funds sent to the operator’s wallet might originate from their drainer campaigns or transfers not subject to the percentage split.
Mandiant Warns Of Growing Trend
Mandiant’s report also highlights the availability and low cost of CLINKSINK drainers in underground forums, indicating a growing trend of financially motivated threat actors targeting cryptocurrency users and services.
The rising value of Solana’s native cryptocurrency, SOL, has likely contributed to the surge in CLINKSINK activity. Furthermore, the CLINKSINK source code’s apparent leakage could enable unrelated threat actors to conduct independent draining operations or establish their own DaaS offerings.
As the value of cryptocurrencies continues to rise, Mandiant predicts an increase in financially motivated threat actors conducting drainer operations.
The ease of access and potential profitability of these campaigns make them an attractive prospect for cybercriminals of varying levels of sophistication.
Cryptocurrency users and investors are urged to exercise caution and employ robust security measures to protect their digital assets. Increased awareness and vigilance within the cryptocurrency community will be crucial in mitigating the risks posed by the CLINKSINK drainer and similar threats.
Featured image from Shutterstock, chart from TradingView.com
Crypto catfishers ditch fake exchanges for approval phishing scams

According to on-chain analytics firm Chainalysis, romance scammers increasingly use this method to steal their victim’s hard-earned crypto.
Asked to get a banana, a BAYC owner narrowly avoids a fake Forbes scam

Scammers posing as Forbes journalists have been targeting BAYC holders to set up interviews and distract them while they attempt to steal their apes.
Nansen phishing emails flood crypto investors’ inboxes

On Sept. 22, one of Nansen’s third-party vendors suffered a security breach, which exposed the email addresses of 7% of the system’s users.
OpenSea NFT users report massive email phishing campaign
OpenSea users have reportedly been targeted with a widespread email phishing campaign, including a fake developer API risk alert and a fake NFT offer.
Chinese hackers use fake Skype app to target crypto users in new phishing scam

Crypto security firm SlowMist has discovered several wallet addresses linked to a phishing scam that drained hundreds of thousands of dollars from unsuspecting crypto users.
Singapore Police Issue Warning Over WhatsApp Phishing Scam
Singapore’s police force have issued a warning in relation to a new variant of a phishing scam that involves hackers taking over a victim’s WhatsApp account and contacts.
Crypto wallet Trezor looks into phishing campaign, exec says

Trezor’s brand ambassador Josef Tetek emphasized that the hardware wallet firm never asks for users’ recovery seed, PIN or passphrase.
Scammers create spoof Blockworks site to drain crypto wallets

Phishing scammers have been spreading fake news of a $37 million dollar Uniswap exploit using a convincing fake Blockworks website.
Fantom Foundation Wallets Drained, More Pain For FTM Holders As Prices Tank
Two Fantom Foundation wallets on Ethereum and the Fantom Network have fallen victim to a phishing attack, losing over $650,000, according to reports from CertiK, a blockchain security firm. Another report by “Spreakaway” on X alleges that one of Fantom’s team members also lost $3.4 million.
Fantom Foundation Falls Victim To Phishing Attack
Fantom Foundation is a non-profit organization dedicated to supporting the growth and development of the Fantom ecosystem. On the other hand, Fantom is a scalable, layer-1 blockchain that is compatible with Ethereum. Like the world’s most valuable network, the platform supports the deployment of smart contracts. For clarity, Fantom’s network was not hacked; the foundation’s wallets were compromised.
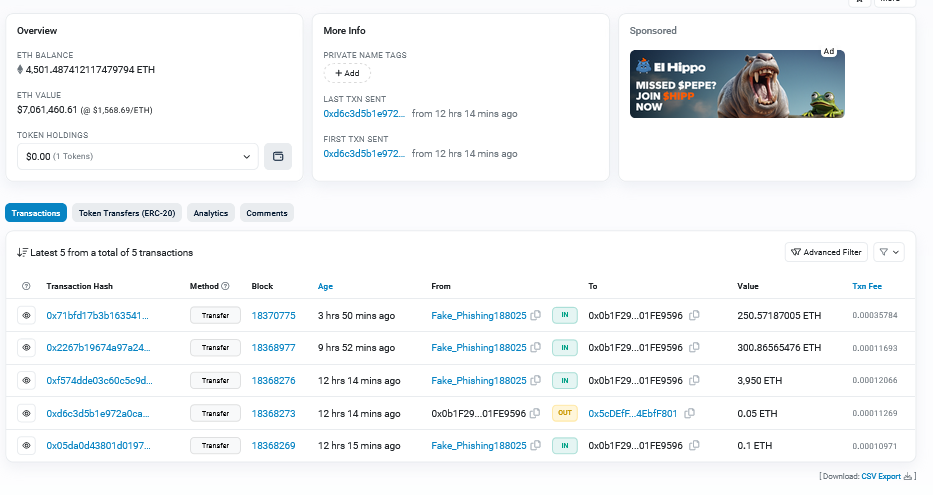
According to CertiK, the Fantom Foundation lost $470,000 on Fantom and at least $187,000 on Ethereum. Following the attack, Etherscan data show that the scammers consolidated funds into one account, holding at least $7 million of various coins. The address has already been marked and identified as a facilitator of multiple phishing campaigns impacting crypto and decentralized finance (DeFi) projects.
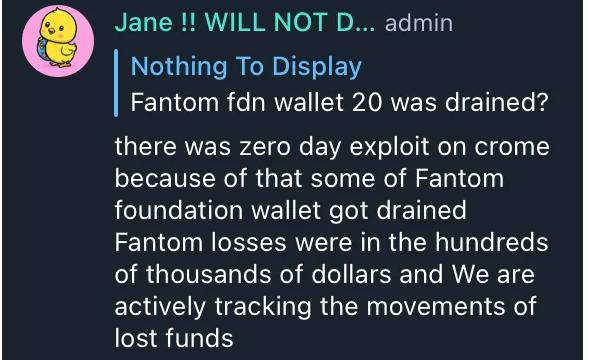
Reports on Reddit show that Fantom Foundation fell victim to a “zero day” exploit on Chrome, a web browser, resulting in the loss of hundreds of thousands worth of FTM. In a screenshot of a Telegram conversation said to have been shared by a Fantom admin, the foundation acknowledged that “some” of their wallets were “drained.” They are actively tracking the movement of stolen funds.
Zero Day Exploit, FTM Sinks Even Lower
A zero-day exploit is a vulnerability unknown to the developer or its tech team, who might be able to fix it. Because the flaw isn’t known to the team, the threat actor can exploit it until it is patched. This is why zero-day exploits can be consequential, especially for DeFi protocols whose infrastructure relies on flawed software.
In the same screenshot shared on Reddit, a representative of Fantom Foundation said they didn’t update their browser to the latest version. The latest Chrome browser update, version 118.0.5993.70, was released on October 11.
Following this news, FTM fell roughly 5% and is now rocking close to multi-month lows. If bears press on, the coin may drop below 2022 lows.
As such, it will reverse all gains made in the first half of 2023. At this year’s peaks, FTM prices rose to as high as $0.65 in February 2023 before contracting to spot rates. The coin is trading at approximately $0.17 and under intense selling pressure.
Galxe replacing 110% of funds users lost in recent front-end hack, over $400K

The platform was the victim of a phishing scam that routed users to a website that drained their wallets after they approved a transaction.
Ordswap urges users to recover keys after losing control of website

Before it was taken down, Ordswap users said the compromised website directed users to a phishing link.
September becomes the biggest month for crypto exploits in 2023: CertiK

The Mixin Network cross-chain protocol accounted for almost two-thirds of the crypto exploit losses in September.
DeFi Protocol Balancer Says Web Front End Is ‘Under Attack’
On-chain data appears to show the attacker has stolen over $200,000 from users.
Celsius creditors flag renewed phishing attacks ahead of bankruptcy plan

Creditors of crypto lender Celsius Network have reported receiving a new flood of phishing emails, likely resulting from two data breaches last year.
Crypto whale loses $24M in staked Ethereum to phishing attack

A significant portion of the stolen funds has been transferred into the fully automatic cryptocurrency exchange FixedFloat.
AI-coded smart contracts may be flawed and ‘fail miserably’ when attacked: CertiK

CertiK’s security chief Kang Li thinks inexperienced programmers using AI tools such as ChatGPT to write smart contracts is a recipe for disaster.
MetaMask scammers take over government websites to target crypto investors

Official government websites from India, Nigeria, Egypt, Colombia, Brazil, Vietnam and other jurisdictions have been found redirecting to fake MetaMask websites.
Terra.money website frozen to prevent more phishing scams

The freeze comes shortly after Terra’s website was compromised over the weekend by hackers who attempted to scam users via phishing attacks.
