Real CoinDesk journalists don’t ask for money. Also, please be wary of links sent from people claiming to work for us.
Crypto Wallets Drained Off $600K Due To Ignored Phishing Attack
On January 23, Wallet Connect and other web3 companies informed their users about a phishing scam using official web3 companies’ email addresses to steal funds from thousands of crypto wallets.
A Massive Phishing Campaign
Wallet Connect took X to notify its community about an authorized email sent from a Wallet Connect-linked email address. This email prompted the receivers to open a link to claim an airdrop, however, the link led to a malicious site and, as Wallet Connect confirmed, it was not issued directly by the team or anyone affiliated. Wallet Connect contacted web3 security and privacy firm Blockaid to investigate the phishing scam further.
We've detected a sophisticated phishing attack impersonating @WalletConnect via a fake email linking to a malicious dapp.
Blockaid enabled wallets are safe.https://t.co/quz9olGrpZ pic.twitter.com/TYS0BjIk2J
— Blockaid (@blockaid_) January 23, 2024
In the following hours, crypto sleuth posted a community alert to inform unaware users that CoinTelegraph, Token Terminal, and De.Fi team emails were also compromised, signaling that a massive and more sophisticated phishing campaign was happening. At the time of the post, around $580K had been stolen.
After investigating, Blockaid later revealed that the attacker “was able to leverage a vulnerability in email service provider MailerLite to impersonate web3 companies.”
Email phishing scams are common among cyber scammers, making users wary of most suspicious links or emails. At the same time, companies and entities advise against opening links that do not come from their official channels. In this case, the attacker was able to trick a vast number of users from these companies as the malicious links came from their official email addresses.
The compromise allowed the attacker to send convincing emails with malicious links attached that led to wallet drainer websites. Specifically, the links led to several malicious dApps that utilize the Angel Drainer Group infrastructure.
The attackers, as Bloackaid explained, took advantage of the data previously provided to Mailer Lite, as it had been given access by these companies to send emails on behalf of these sites’ domains before, specifically using pre-existing DNS records, as detailed in the thread:
Specifically, they used “dangling dns” records which were created and associated with Mailer Lite (previously used by these companies). After closing their accounts these DNS records remain active, giving attackers the opportunity to claim and impersonate these accounts. pic.twitter.com/cbTpc5MXu1
— Blockaid (@blockaid_) January 23, 2024
MailerLite Explains Security Breach
The explanation later came Via an email, where MailerLite explained that the investigation showed that a member of their customer support team inadvertently became the initial point of the compromise. As the email explains:
The team member, responding to a customer inquiry via our support portal, clicked on an image that was deceptively linked to a fraudulent Google sign-in page. Mistakenly entering their credentials there, the perpetrator(s) gained access to their account. The intrusion was inadvertently authenticated by the team member through a mobile phone confirmation, believing it to be a legitimate access attempt. This breach enabled the perpetrators) to penetrate our internal admin panel.
MailerLite further adds that the attacker reset the password for a specific user on the admin panel to consolidate the unauthorized control further. This control gave them access to 117 accounts, of which they only focused on cryptocurrency-related accounts for the phishing campaign attack.
An anonymous Reddit user posted an analysis of the situation and gave a closer look at the attacker’s transactions. The user revealed:
One victim wallet appears to have lost 2.64M worth of XB Tokens. I’m showing about 2.7M sitting in the phishing wallet of 0xe7D13137923142A0424771E1778865b88752B3c7, while 518.75K went to 0xef3d9A1a4Bf6E042F5aaebe620B5cF327ea05d4D.
The user stated that most stolen funds were in the first phishing address. At the same time, approximately $520,000 worth of ETH were sent to privacy protocol Railgun, and he believes that they will soon be moved through another mixer or exchange.

Massive Solana Heist: CLINKSINK Drainer Campaigns Swipe Nearly $1M Worth Of SOL
In a recent report released by Mandiant, a threat intelligence and cybersecurity company, alarming details have emerged about the widespread exploitation of Solana users through a campaign known as CLINKSINK.
The report sheds light on the nature of these drainer campaigns, which have resulted in the loss of nearly $1 million worth of SOL tokens.
CLINKSINK Campaign Targets Solana Investors
According to the report, The CLINKSINK campaign, identified by Mandiant, involves malicious actors leveraging drainers – malicious scripts and smart contracts – to steal funds and digital assets, including non-fungible tokens (NFTs), from unsuspecting victims’ cryptocurrency wallets.
These campaigns have been active since December 2023 and have employed at least 35 affiliate IDs associated with a drainer-as-a-service (DaaS) utilizing CLINKSINK.
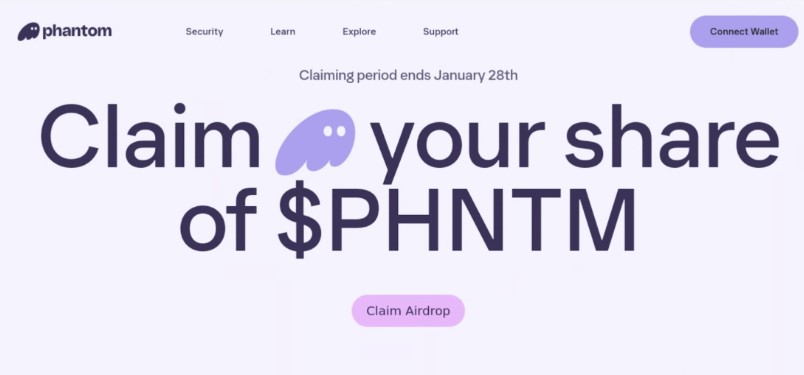
The modus operandi of the CLINKSINK campaign involves distributing cryptocurrency-themed phishing pages through social media platforms like X and chat applications like Discord.
These pages, masquerading as legitimate cryptocurrency resources like Phantom, DappRadar, and BONK, entice victims to interact with the CLINKSINK drainer. Once victims connect their wallets to claim an alleged token airdrop, they are prompted to sign a transaction that allows the drainer service to siphon funds from their wallets.
Mandiant’s investigation revealed that the stolen funds are divided between the affiliate and the service operator(s) based on a predetermined percentage.
The analysis indicates that, on average, 80% of the stolen funds go to the affiliate, while the remaining 20% go to the operator(s). However, the operator’s cut can vary between 5% and 25%, potentially influenced by factors such as partnerships or reduced fees for successful affiliates.
Since the end of December 2023, at least 1,491 SOL tokens and numerous underlying tokens, with a combined value of over $180,000, were traced to a specific Solana address associated with the DaaS operator.
Based on this data, Mandiant estimates that these recent campaigns have stolen at least $900,000 in digital assets. However, it is important to note that some of the funds sent to the operator’s wallet might originate from their drainer campaigns or transfers not subject to the percentage split.
Mandiant Warns Of Growing Trend
Mandiant’s report also highlights the availability and low cost of CLINKSINK drainers in underground forums, indicating a growing trend of financially motivated threat actors targeting cryptocurrency users and services.
The rising value of Solana’s native cryptocurrency, SOL, has likely contributed to the surge in CLINKSINK activity. Furthermore, the CLINKSINK source code’s apparent leakage could enable unrelated threat actors to conduct independent draining operations or establish their own DaaS offerings.
As the value of cryptocurrencies continues to rise, Mandiant predicts an increase in financially motivated threat actors conducting drainer operations.
The ease of access and potential profitability of these campaigns make them an attractive prospect for cybercriminals of varying levels of sophistication.
Cryptocurrency users and investors are urged to exercise caution and employ robust security measures to protect their digital assets. Increased awareness and vigilance within the cryptocurrency community will be crucial in mitigating the risks posed by the CLINKSINK drainer and similar threats.
Featured image from Shutterstock, chart from TradingView.com
Crypto VC Polychain Capital confirms founder’s X account hacked

Polychain Capital is urging users to stay away from the X account of its founder, Olaf Carlson-Wee, as it is posting phishing links.
Inferno Drainer says it’s shutting down after helping steal $70M in crypto

“We hope you can remember us as the best drainer that has ever existed,” wrote the scam-as-a-service wallet drainer.
Singapore Police Issue Warning Over WhatsApp Phishing Scam
Singapore’s police force have issued a warning in relation to a new variant of a phishing scam that involves hackers taking over a victim’s WhatsApp account and contacts.
Friend.tech users blame SIM swaps after more than 100 ETH drained in a week

In a short period of time, four friend.tech users reported their accounts were compromised and drained after hackers seized control of their mobile numbers.
Notorious Monkey Drainer crypto scammer says they’re ‘shutting down’

The scammer behind the crypto wallet draining kit even recommended an alternative and gave advice to budding cybercriminals.
Sam Bankman-Fried deepfake attempts to scam investors impacted by FTX

A faked video the FTX founder created by scammers has circulated on Twitter with users poking fun at its poor production quality.
Beeple’s Discord URL ‘hijacked,’ directing users to wallet drainer

Other users in the crypto Twitter Community believe lax security management is to blame for the latest phishing scam aimed at Beeple’s fans and followers.
British Army’s social media accounts hacked by crypto scammers

Hackers had access to multiple official social media accounts of the British Army for nearly four hours, when they posted crypto phishing links and scams.
Targeted phishing scam nets $438K in crypto and NFTs from hacked Beeple account

Links posted to a fake Louis Vuitton non-fungible token (NFT) raffle were made to capitalize on a recent real collaboration between Beeple and the luxury fashion brand.
Rare Bears Discord phishing attack nabs $800K in NFTs

The account of a moderator from the non-fungible token project was compromised in the attack, posting a phishing link that drained user wallets.
Ledger faces class action from phishing scam victims

Ledger and Shopify are facing a class-action lawsuit over sensitive information regarding 270,000 of Ledger’s customers’ that was stolen by Shopify employees.
Prosecutors Detail Russians’ Crypto Phishing Scheme in Forfeiture Suit
The alleged hackers also manipulated NEO’s Gas market with a $5 million crypto infusion.
Kaspersky: Cryptocurrency Scammers Stole $2.3 Million in Q2
Cybercriminals earned more than $2.3 million from cryptocurrency scams during the second quarter of 2018, a new study reports.